Most of security breaches happen because of lack of effort on security prioritization.
Most corporate security departments are engaged with procedural burden which is documented in policies and is required by management. Instead of fulfilling their direct duties, which is to protect business from cyber threats. Why is it so? Because execution of procedures is easier, as well as it is easier for them to justify their existence in such a way. We exist because of PCI DSS, GDPR, SOX, ISO 27k etc.
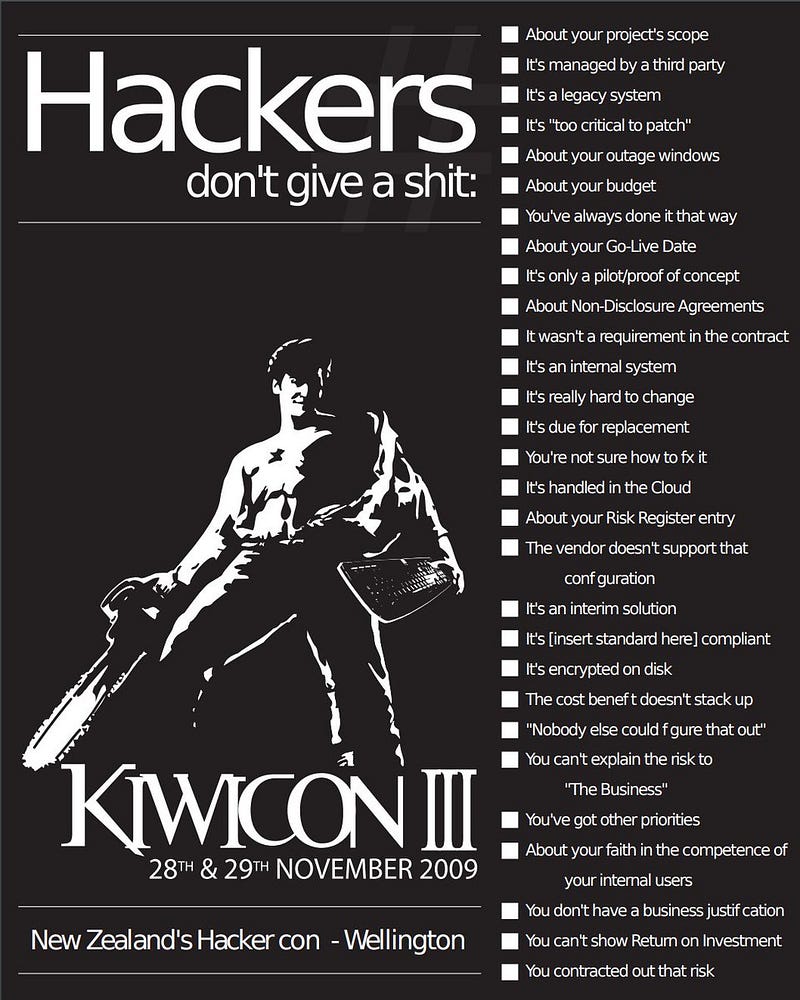
Most of the companies that were hacked had some sort of security policy. Why have they suffered a breach? Because paper doesn’t protect from hackers. Only rules and actions protect from hackers and malicious software (aka viruses). Rules and actions separately — do not protect, only both combined: rules + actions. Moreover, you don’t have to invent neither rules nor actions — they were invented a long time ago and are publicly available.
Based on my experience, I’ve reached a conclusion that an enterprise cybersecurity practice should start neither from a corporate security policy nor from a new firewall or antivirus. Management gets “paper tigers” and “blinking boxes” well, however this is a bad, even unprofessional start. The right thing would be to start from applying simple rules and actions and demonstrate their effectiveness. We must not have outdated OS versions in our network. All users must have long and strong passwords. Network and resources must be segmented based on business needs. Remote access should be supplied with two factor authentication. Interactive administrative access to systems should be prohibited. And so on, and so forth. One rule at a time, one action after another.
And then you will have chances not to become a victim.